TRANSNATIONAL REPRESSION
Phony whistleblowers, fake journalists and cyber spies: ICIJ network targeted after China Targets probe
Shortly after publication, a slew of fake ICIJ reporters approached journalists, Taiwanese officials, and human rights advocates seeking sensitive data. With Citizen Lab, we investigated

In May 2025, Kuochun Hung, the chief operating officer of the Taiwanese media outlet Watchout, received an email from someone purporting to be Yi-Shan Chen, a well-regarded local reporter.
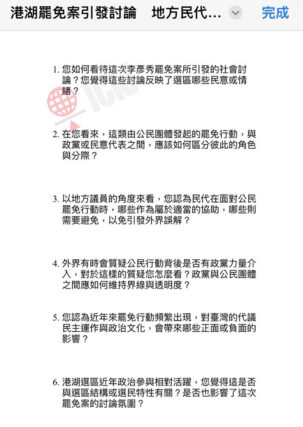
“Chen” claimed to be working for the International Consortium of Investigative Journalists and was requesting an interview with Hung on a range of topics: then pending impeachment proceedings against Taiwan’s president, the island’s divided government, and Watchout’s planned events with members of civil society groups.
Hung, whose media outlet monitors information manipulation, found the email unusual.
“The topic and questions in the invitation email [were] too entry-level for a senior journalist,” Hung told ICIJ. What’s more, Chen’s name was spelled in English, instead of the original Chinese, and the email address didn’t include ICIJ’s official domain.
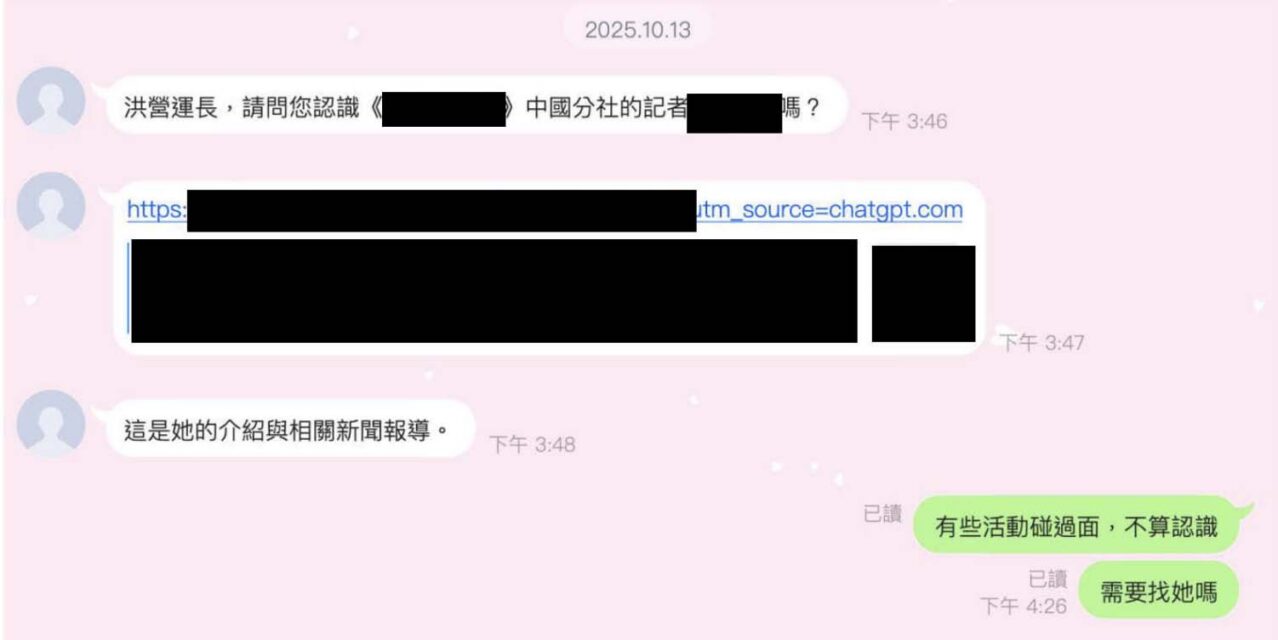
Hung decided to find out more and started interacting with “Chen” on LINE, a popular messaging app in Taiwan.
The person, who used Chen’s name and photo in their handle, told Hung that an American journalist from ICIJ would meet him in Taipei for the interview and sent a link to what looked like an ICIJ webpage with the reporter’s photo. Hung noticed it wasn’t ICIJ’s real website. The fake Chen also sent Hung another link she said would direct him to a list of questions, adding: “For journalists, information security is truly very important,” a warning most journalists would find superfluous.
Hung didn’t click.
“I played stupid,” he said. “And then she gave up.”

Hung, who knows malicious links can be used to steal personal information, suspects that his interlocutor was a Chinese spy impersonating the real Yi-Shan Chen, a financial journalist and editor-in-chief of CommonWealth magazine — a trusted news source in Taiwan. As a member of ICIJ’s network, Chen has partnered with the Washington, D.C.-based news organization on many investigations, but is not an employee.
“They are spies with cyber capabilities,” Hung said. “Their goal is political.”
The real Chen told ICIJ in an interview that she shared Hung’s concerns. “Ironically, they are using the credibility of the investigative reporters to [collect] intelligence,” she said. Chen reported the impersonation attempt to Taiwanese authorities.
Now, an investigation by ICIJ, with the help of cybersecurity analysts at Toronto University’s Citizen Lab, has found that the incident was part of a sophisticated offensive strategy against ICIJ and its network following the 2025 publication of China Targets. The ICIJ-led exposé, in collaboration with 42 media outlets, revealed Beijing’s tactics to threaten, coerce and intimidate regime critics overseas.
Citizen Lab, which specializes in investigating digital threats, analyzed suspicious emails sent to this ICIJ reporter and other messages sent by ICIJ impersonators to targets in Asia, Europe and the United States. Detailing the findings in a report released today, one year after China Targets was published, the analysts said the attacks against the ICIJ network are part of “a wide-ranging campaign” aimed at stealing private information from entities of interest to the Chinese government. Those include Uyghur, Tibetan, Taiwanese, and Hong Kong diaspora activists, as well as journalists from ICIJ and elsewhere who report on activities related to these groups.
Rebekah Brown, who led the Citizen Lab investigation, said it indicated that so-called threat actors linked to the Chinese government had used surreptitious means to learn who ICIJ was talking to.
“We suspect that there was some sort of directive [saying] that it’s very important to know, especially after the China Targets report, who’s talking to you, what are you working on now? How can they intervene? How can they stop this narrative from growing?” Brown said. “That results in these targeted digital intrusions, both on [ICIJ] and on a lot of the communities who might possibly be telling you and other journalists things that the government doesn’t want.”
While the probe couldn’t identify which government agency may have given the orders, “we are highly confident that this is China,” said Brown, who in the past worked as a network warfare analyst for the U.S. government.
A Taiwanese national security official told CommonWealth magazine that the attacks are similar to others identified as part of a Chinese state-sponsored espionage operation.
In response to questions from ICIJ, a spokesperson for the Chinese Embassy in Washington, D.C., said that “China has always opposed and cracked down on any form of cyber attacks” and that transnational repression is “a completely fabricated narrative maliciously concocted by certain countries and organizations in an attempt to smear China.”
The Citizen Lab analysts found more than 100 domains targeting at least a dozen individuals with the aim of stealing credentials, most likely to enable further surveillance, device compromise and coordinated harassment campaigns.
ICIJ spoke to some of the targets, including a Taiwanese foreign ministry official, who was approached by someone impersonating an ICIJ reporter. The imposter told the official that his contact information was provided by “headquarters” — a term journalists generally don’t use.
Citizen Lab found several errors suggesting that the attackers may have been involved in a “high volume” of attacks and used artificial intelligence to automate them, identify targets and generate messages without much oversight.
“It’s yet again a confirmation that the Chinese state continues to be deeply concerned about controlling the narrative about itself overseas and repressing, surveilling or harassing individuals who are challenging their preferred narrative,” said Emile Dirks, a researcher of Chinese surveillance and contributor to the Citizen Lab report.
ChatGPT links and other clues
A few weeks after Hung declined to click on the first suspicious link, the fake Chen contacted him again, out of the blue, this time asking for information about religious organizations in Taiwan and the latest White House national security strategy.
He noticed that most of the messages were sent only during office hours in Taiwan or China’s time zones, another hint that the person wasn’t a real reporter.
“You know how real journalists are,” Hung said. “There is no time off!”
He then spotted yet another oddity that still makes him chuckle. During one of the interactions, the fake journalist sent him a link to the bio page of a China-based correspondent for an American newspaper. The link ended with “source=chatgpt.com.” For Hung, it was clear: the suspected spy was using ChatGPT to research their targets. Brown told ICIJ that it was a significant discovery because previous inquiries by ChatGPT’s creator, OpenAI, revealed that Chinese law enforcement used the system to plan and create “cyber special operations” against dissidents and regime critics.
Finally, one day last December, a giveaway. After Hung complained that his phone wasn’t working well, the fake Chen offered to send him a brand new Samsung smartphone.
Hung accepted, curious to see if the imposter would somehow rig the device. He asked them to send the phone to a convenience store in central Taipei — a common way of sending and receiving packages in the city. Instead, fake Chen told him someone would deliver it to the store personally.
The delivery was not successful, Hung said, because the store didn’t accept private packages. Hung provided a different address but no phone ever arrived, he said.
According to CommonWealth magazine, at least five people in Taiwan, including one city councilor and one legislative assistant, were approached by someone purporting to be Chen. Two of them were offered brand-new phones but never received the devices.
Taiwan’s Ministry of Justice Investigation Bureau, the country’s law enforcement agency, told the magazine that it is currently investigating the reports.
The whistleblower
While the fake Chen was approaching targets in Taiwan, thousands of miles away from Taipei, a Taiwanese foreign ministry official in Europe and U.S.-based advocates, who work with members of the Uyghur minority and Chinese activists, were receiving what appeared to be interview requests from ICIJ reporters. And ICIJ reporters themselves received emails from people purporting to be Chinese whistleblowers ready to provide newsworthy tips.
One email, in particular, stood out.
In June 2025, this reporter received an email from someone named Bai Bin, who described himself as a former judicial assistant from Beijing. “Bai” was offering to share documentary evidence that would help unmask a $10 million embezzlement scheme allegedly involving figures in China’s top anti-graft agency.
In the email written in English, the purported whistleblower said that the scheme had been organized at “the top,” and he had fled to Japan with secret documents.
Last year, Chinese media reported that a person named Bai Bin, who was once a promising judicial assistant in the enforcement division of a Beijing court, had stolen more than $4 million and fled the country. In his email, the purported whistleblower insisted that the allegations against him were part of a cover-up for the crime he wanted to expose.
“Bai” praised ICIJ’s work and pledged to help.
His first email arrived on June 20, 2025, a few weeks after ICIJ published China Targets, which included an article detailing how Chinese authorities had used Interpol red notices to force a politically connected businessman to return to China. “Bai” ’s email was offering information on the same anti-graft agency mentioned in the ICIJ article.
But something about his message was off. The tone was oddly formal, with phrases that sounded as though they were generated by AI. An em dash (—) was used to end sentences, a feature of some AI systems’ writing style. And even though the body of the email was purportedly from Bai, the name on the email account belonged to someone completely different — a former U.S. diplomat with expertise on Chinese and Taiwanese affairs. The email included a link that “Bai” said led to an archive full of confidential records.
ICIJ concluded that the link was likely malicious, the whistleblower a fake, and the email a clumsy attempt to steal the reporter’s login details to access source information and other sensitive data.
She didn’t click. But hoping to learn who might be behind the phony whistleblower, she did respond. After exchanging more than a dozen emails, the fake Bai grew frustrated with the reporter’s hesitation.
“I’m quite frustrated,” he wrote in a long email. “I’ve already spent a lot of time and energy trying to make this work.” ICIJ’s attempts to reach the real Bai Bin were unsuccessful.
Brown, the lead Citizen Lab researcher, said that the fake whistleblower’s story and engagement showed the attack was sophisticated, but that the group behind it only had one trick at its disposal, known as OAuth phishing. These cyberattacks take victims to a Microsoft or Google sign-in page that looks legitimate but authorizes a malicious application to read emails, send messages and access files.
“Even though they have a lot of resources to put into developing a persona and developing a story they think is enticing to you, on the technical level, they basically had that OAuth phishing kit to try and get into and like that was it,” Brown said.
These limitations suggest the attackers were private contractors in China’s ever-growing commercial hacking industry working for a government agency, according to Brown and a Taiwanese security official interviewed by CommonWealth magazine.
The attack shared similarities with another type of campaign called spear phishing, which cybersecurity analysts previously attributed to Chinese state-sponsored actors who target people with personalized messages to trick them into divulging sensitive data.
“In the case of state-sponsored credential theft,” the Citizen Lab report said, “the attacker can gain insight into topics of state-interest, spread disinformation via the compromised account, or use the credentials in future attacks against the target or their contacts.”
According to Dirks, the Chinese surveillance researcher, even if the attack is unsuccessful, campaigns like these can have a “chilling effect.”
“It sends a message to people like yourself and your colleagues, to members of diaspora communities, to human rights organizations that they are being watched, they are being monitored and that they are in the crosshairs of Beijing.”
Digital transnational repression
Digital transnational repression — the use of online technologies for targeted intimidation, threats and surveillance — is a common weapon in the hands of autocratic regimes such as China and Russia, according to a recent European Parliament study. In China, hackers-for-hire compete to support the government’s cyber operations, from monitoring negative social media posts to selling spyware, phishing kits and other offensive cyber tools.
Last year, ICIJ and its media partners interviewed more than 100 targets of Beijing’s repression and found about half of them had been victims of online smear campaigns, hacking attempts, or phishing campaigns seeking to steal their information.
Among them was Jiang Shengda, a Paris-based artist and activist whose family in Beijing has often been visited and interrogated by Chinese security officials demanding that Jiang stop his activism.

After ICIJ exposed details of the officials’ intimidation tactics against Jiang’s family last year, the activist noticed an uptick in cyberattacks targeting his email account.
Jiang, who also collaborates with a Chinese dissident considered a “key individual” — or threat — by Beijing, said he receives about two to four phishing emails a day from accounts mimicking supermarket chains or postal services.
Jiang said he has informed European authorities about the “harassment” campaign against him and now helps other Chinese dissidents protect against cyber threats.
“This is not just a personal issue,” he said, “but a pressure shared across the entire community.”
For Brown and her team at Citizen Lab, the work isn’t over.
They will continue to collect evidence about attacks and perpetrators, hoping to inform the public as well as policymakers and government leaders, Brown said.
“By more people knowing that this is a coordinated effort and it’s not isolated, we’ll be able to connect more dots and identify what’s actually going on,” she said. “That will help us both to prevent and detect it better, but also it will give people in leadership maybe some way to hold accountability.”
Note: ICIJ staff email addresses include the domain icij.org. If you believe an ICIJ impersonator has approached you, please do not engage and notify us at contact@icij.org.